Five Things to Know about History’s First Malware
In 1988, the use of computers, let alone the programming of them, had not yet taken foothold in the US. It wouldn’t be until a few years later that word processing applications and other familiar interfaces became familiar. Still attached to academia and government, the 60,000 or so computers connected to the internet — rather, its precursor the ARPANET — were a sort of experimental and intellectual playground for those developing the technology and learning it.
On November 2nd of that year, however, the very way people conceived of networks and the internet changed forever. The atmosphere of a brainy, optimistic fellowship gave way to the notion that the internet was as much hazardous territory as it was fertile ground for learning and doing. That day, the tens of thousands of computers were rapidly, and seemingly simultaneously, exposed to a self-replicating computer program we now call a worm.
The Morris worm, named for its creator, Cornell University student Robert Tappan Morris, rapidly infected the limited (by today’s standards) computers connected to the internet. An estimated 6,000 machines, depleted of their resources as the worm depleted computing resources, shut down and were rendered inoperable. Today this is the opposite of what it was then: plausible, fathomable, even expected. For those who were affected by the worm, it was a bewildering and frightening experience.
Here’s what you need to know about the Morris worm, history’s first malware.
1. The Morris worm attack was one of the most significant events in the history of computer science.
Many developments in the history of computer science caused their early influencers, and society as a whole, to rethink the role they would play. Charles Babbage’s difference engine (1820s) showed that mathematics and other simple calculations were destined to be automated. The Digital Revolution (late 1950s-1970s) moved us away from analog and mechanical computing towards the next era of power, performance and efficiency. The Morris worm, on the other hand, was the first instance of a networked computer or group of computers’ helplessness. With the Morris worm, “vulnerability”, as we now term this sort of jeopardy, quickly occupied the mindset of all who were associated with computing: scientists, developers, students, and government officials. November 2, 1988 is the day computer science lost its innocence. Today no serious player in any aspect of computing — hardware to software, consumer to enterprise — thinks of computers and networks as safe, or regards digital “information security” as optional.
2. The Morris worm was intended to be an intellectual exercise, or a pen-test, but it went awry.
Robert Morris, like his late 1980s contemporaries, was as interested to learn the potential of computers as he was in their substance. A programming student at Cornell, he developed his self-replicating program to test the boundaries of the network — a sort of penetration testing. While opinions may still vary on his motives, one fact still stands: he concealed his activities by hacking into the Massachusetts Institute of Technology (MIT) network to launch his worm, attempting to cover his tracks. A friend of his, accounts say, tipped off The New York Times giving them Morris’s initials. He paid a price for his actions. In 1989, the first to be indicted under the US Computer Fraud and Abuse Act (CFAA), he was sentenced to a fine of $10,050 plus costs of his supervision, three years of probation, and 400 hours of community service. Complicating matters, Robert Morris was the son of a respected Bell Labs and US National Security Agency (NSA). The story did not end there. The younger Morris went on to become a renowned academic, tech founder and venture capitalist. He is currently a tenured professor of computer science and artificial intelligence at MIT’s Electrical Engineering & Computer Science department.
3. The Morris worm functioned as a denial-of-service (DoS) attack.
The Morris worm spread by exploiting vulnerabilities in UNIX sendmail (using a backdoor), finger (through buffer overflow), and rsh/rexec (to explore whether it could operate). The worm also worked by guessing weak passwords, as it contained 900 passwords and could use names of account holders to brute force possible passwords. Reinfection and compounded repetition were a prime aspect. The end result was occupying the machine’s resources until it shut down, much in the way a denial-of-service (DoS) or distributed denial-of-service (DDoS) attack swarms a network with a series of worthless requests until service is halted. Before infecting a new machine, the worm verified if it had already been infected. If it was, the worm would re-infect it 1 in 7 times. This was to accelerate its spread but also to prevent a user from mimicking a worm process to feign infection. In all, 6,000 or so computers were infected. Experts recall that many days of chaotic internet chatboard discussion ensued, and that it took two days to fully remove the Morris worm from each machine. The US Government Accountability Office (GAO) estimated Morris worm damage to be in the very broad range of $100,000–$10,000,000.
4. An identical Morris worm attack is no longer viable.
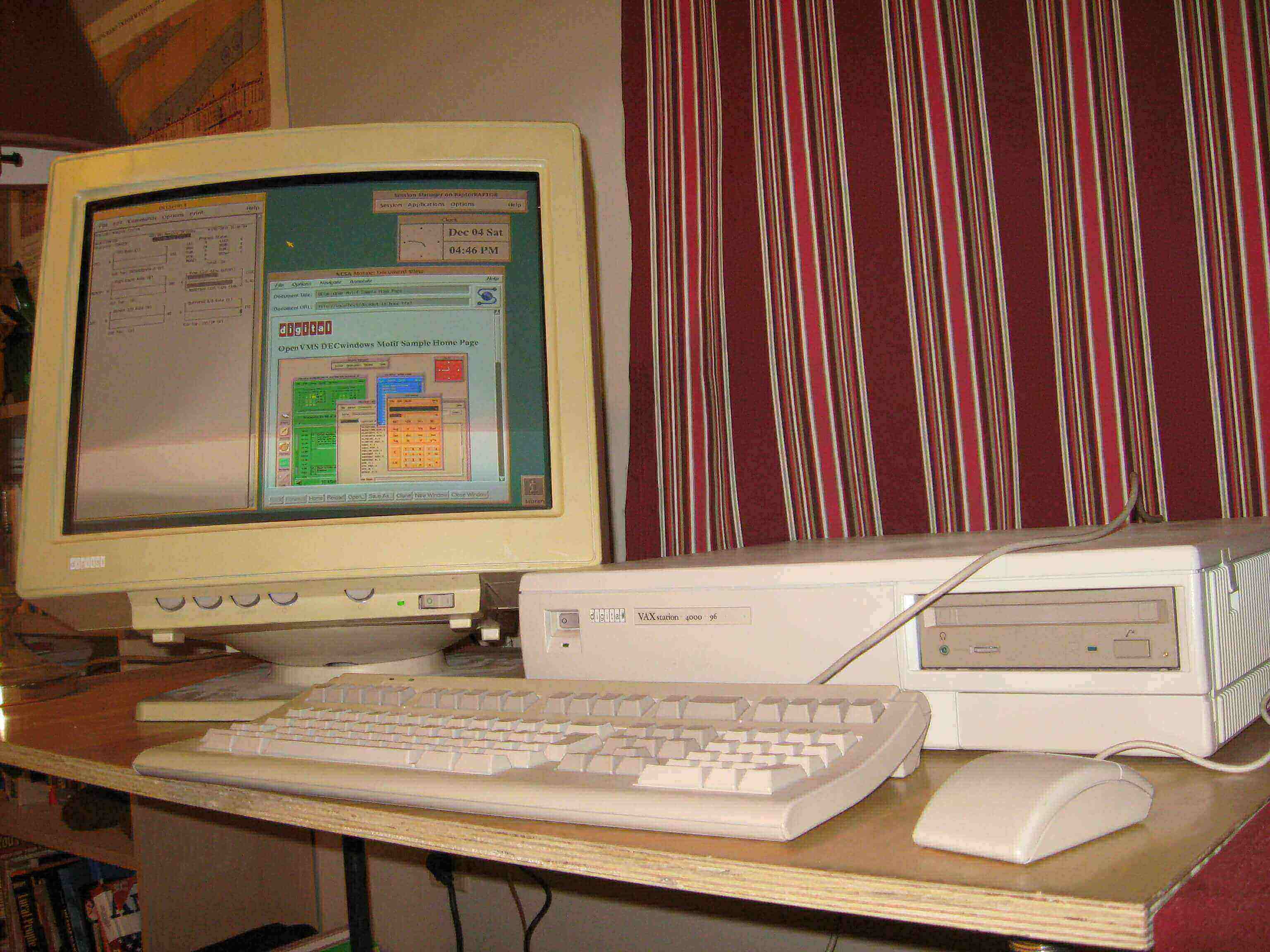
Experts say that at the time of the Morris worm, most people who operated computers were using DEC VAX ones running UNIX. A distinct “monoculture” persisted that would seem alien to today’s diverse landscape of various operating systems, OEMs, devices, software standards, communication protocols, and so forth. Attitudes since then have shifted towards a “security first” attitude, particularly in the enterprise setting. From this alone comes an entirely new sphere of security products, practices, laws, norms, planning, response, detection and other things that simply did not exist during the worm attack — they emerged from it. Closer to the user and each machine, a vulnerability the Morris worm attacked was weak passwords. Identity and access management (IAM), a whole field in itself, today ensures that password usage and curation — and their elimination! — are front and center. Today computing and the internet in 1988 are no longer the cooperative milieu or playground they were — it’s a serious atmosphere comprised of many focused, vigilant security practitioners.
5. The Morris worm ushered in trust as we know it, and today ‘Zero Trust’ dominates.
Three decades after the Morris worm’s significant event in the field’s history, the #1 lesson it taught is that the person(s) administering a network must verify those seeking access. Not only did the Morris worm cause the community of 60,000 users of the then-internet’s machines to lose innocence. It destroyed their collective assumption their own good intentions should be extended to others — and as a result, themselves. Suspicion, the lack of trust that permeates computing — on the unofficial scale of less on the consumer side, more on the enterprise, and high for the “mission-critical” — is now the norm. Today, the idea of Zero Trust is compounding that attitude, born circa 1988. The road toward verifying users and all kinds of access is trending in one direction: less (or no) trust.
The Morris worm has been called the "Great Worm". This is a nod to Tolkein’s Long-worms (or dragons), Scatha and Glaurung, the comparison being that the Morris worm had great destructive power. Certainly the worm caused devastation in its day, and for its day, and gave birth to fear.
That’s five things you now know about the Morris worm. To learn more, watch the Computerphile video featuring Dr. Julian Onions, noted programmer and astrophysicist from the UK.
