Platform HYPR + Ping Identity
HYPR + Ping Identity
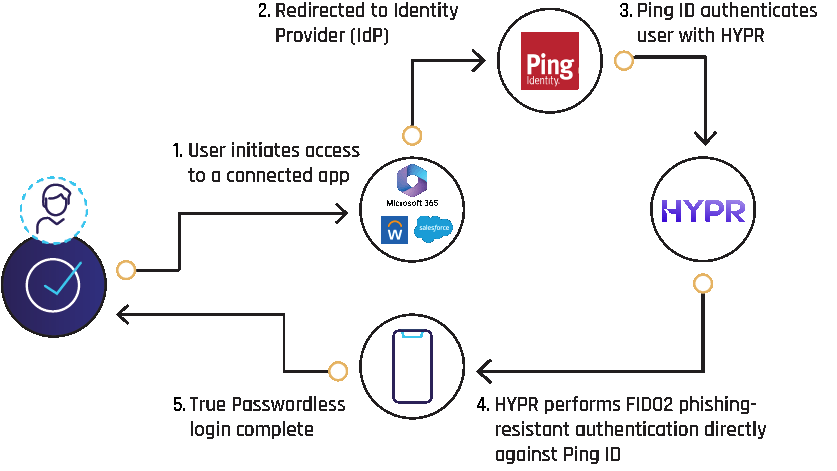
Ping Identity offers an identity security platform that addresses both customers and workforce users. With HYPR, organizations can finally introduce fast and easy passwordless multi-factor authentication (MFA) to their PingFederate environment.

Extend Your Investment in Ping SSO
Make the most out of your Ping Identity solutions. As a Ping Technology Alliance Partner, HYPR integrates seamlessly with your existing infrastructure.
HYPR's True Passwordless Ping Federate Integration Provides:
- Interoperability with FIDO U2F security keys such as YubiKey, and built-in platform authenticators such as Windows Hello.
- Cross-cloud, cross-platform passwordless login to Windows, MacOS, Linux and VDI workstations.
- Full protection against man-in-the-middle (MitM), credential stuffing, phishing, and push bombing attacks.
- Ease of deployment and use by admins and end users alike.

Secure, Single Action Login to Ping Identity
Replace passwords with passkeys. From Azure, you authenticate once using HYPR Enterprise Passkeys, to gain access to Ping Identity and all downstream apps.
If you already signed into your desktop with HYPR, then the authenticated identity is automatically passed to Ping. No additional verification steps, unless step-up authentication is required.
Reduce Risks and Costs
Eliminate vulnerabilities and password reset costs with mobile-first authentication.
Deploy in Your Own App
Speed time-to-market with fast integration using HYPR’s mobile and web SDKs.
Secure & Convenient
Provide seamless access without the hassle of multiple sign-ons and passwords
Request a Demo
Experience passwordless MFA that secures and empowers your business. See what identity verification built for the workforce looks like. Learn how comprehensive Identity Assurance protects the entire identity lifecycle.
Fill out the form to get a demo from an identity security expert, customized around your organization’s environment and needs.

