Platform HYPR + YubiKey Integration
YubiKey Management and Identity Verification
HYPR + Yubico Integration
Combine FIDO Certified physical and virtual tokens for a secure, consistent user experience that eliminates passwords, reduces risk, meets compliance requirements, and improves efficiency.

Simplify YubiKey Provisioning
HYPR and Yubico have expanded their long-standing partnership to make secure YubiKey provisioning and deployment effortless at scale. The new integration connects HYPR Affirm, our identity verification orchestration product, with Yubico’s provisioning capabilities, ensuring every YubiKey is issued to a verified individual, fully aligned with NIST 800-63-3 assurance standards.
With HYPR Affirm, organizations can now verify identity, pre-register credentials, and activate YubiKeys through an automated, auditable workflow that eliminates manual handoffs and accelerates deployment across remote and hybrid teams.
.jpg?width=1632&height=522&name=Yubico-1%20(1).jpg)
1. Ship: YubiKeys are assigned and shipped directly to employees or contractors on file.
2. Notify: Recipients receive an email prompting them to begin HYPR Affirm’s secure identity verification.
3. Verify: Employees complete a short identity check, including document, biometric, and liveness verification.
4. Authorize: Once verified, a unique PIN is issued to activate the pre-registered YubiKey.
5. Activate: The YubiKey is ready to use, fully bound to a verified identity and compliant with enterprise security policy.
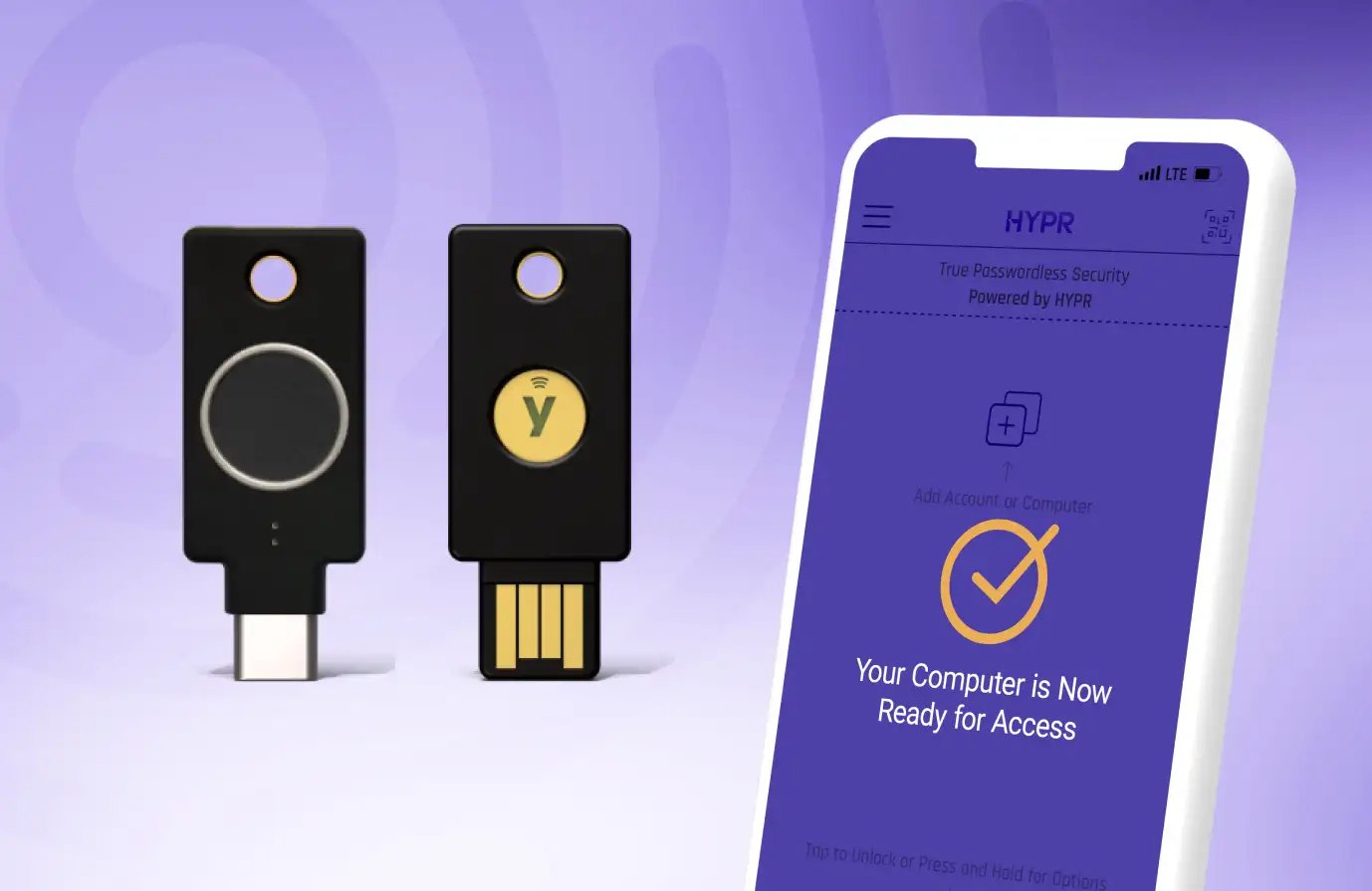
Multi-Protocol YubiKey Bio Series
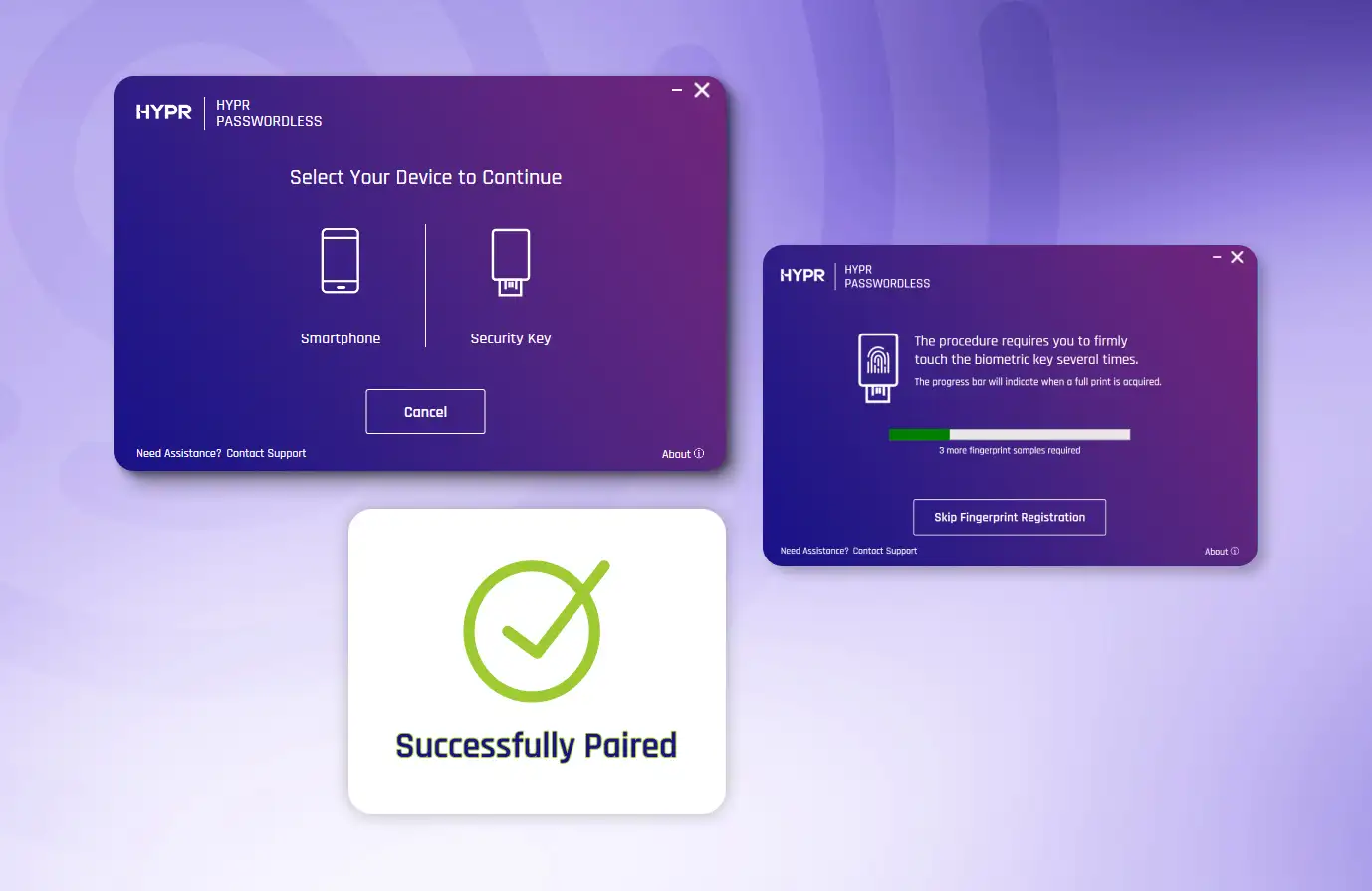
Seamless Onboarding Only With HYPR
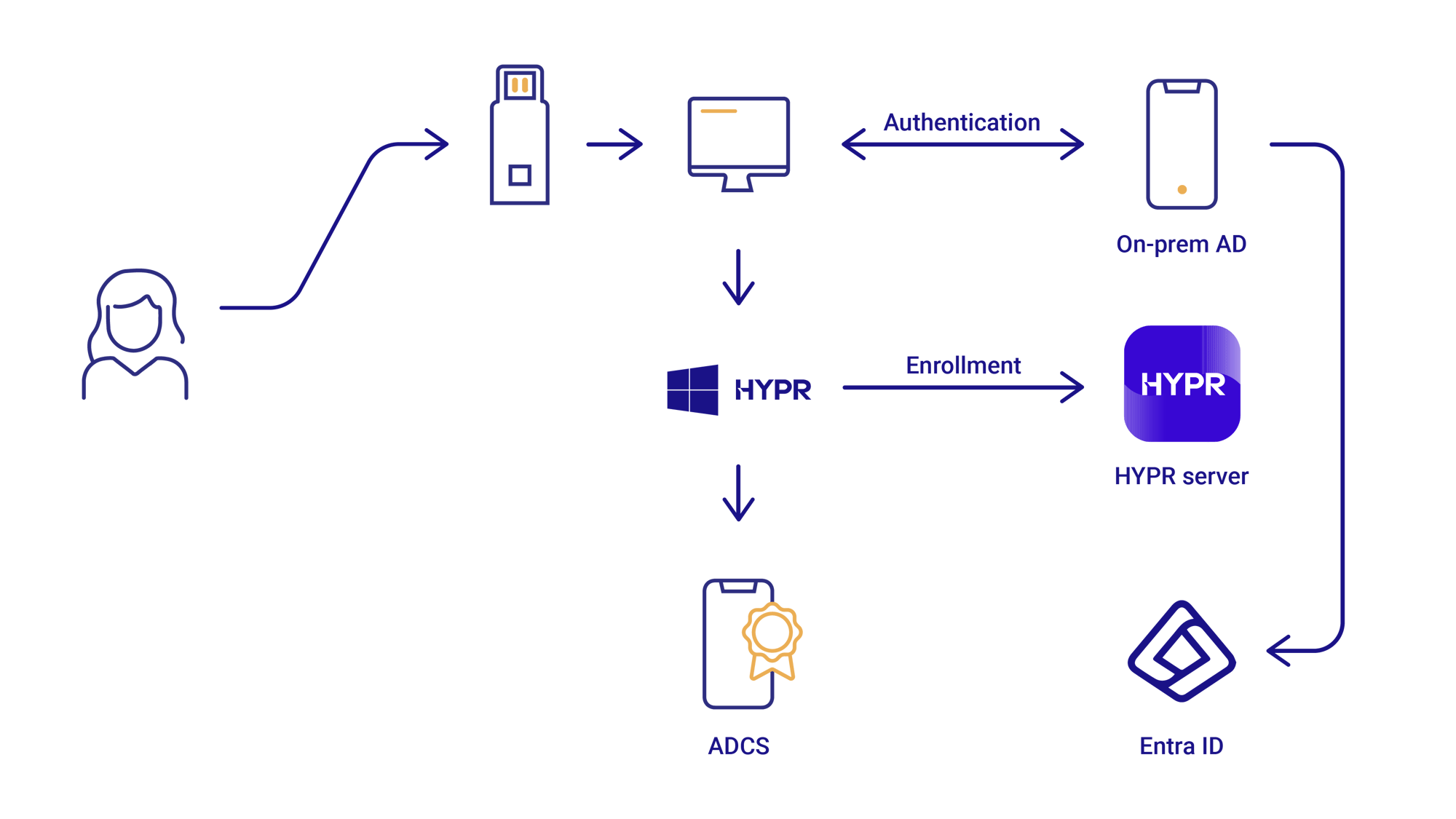
Yubico has enhanced its YubiKey Bio Series to include the YubiKey Bio - Multi-protocol Edition, with support for FIDO and Smart Card/PIV protocols. With HYPR as the sole inaugural partner, the new multi-protocol keys provide fast, convenient authentication that helps organizations accelerate their passwordless transition:
- Desktop login on Microsoft Windows using Smart Card/PIV with fingerprint
- Web authentication with FIDO2 using the same biometrics or PIN as desktop login
- Enrollment to workstations using HYPR to provision and centrally manage credentials
Extend and Enhance Your YubiKey Investment
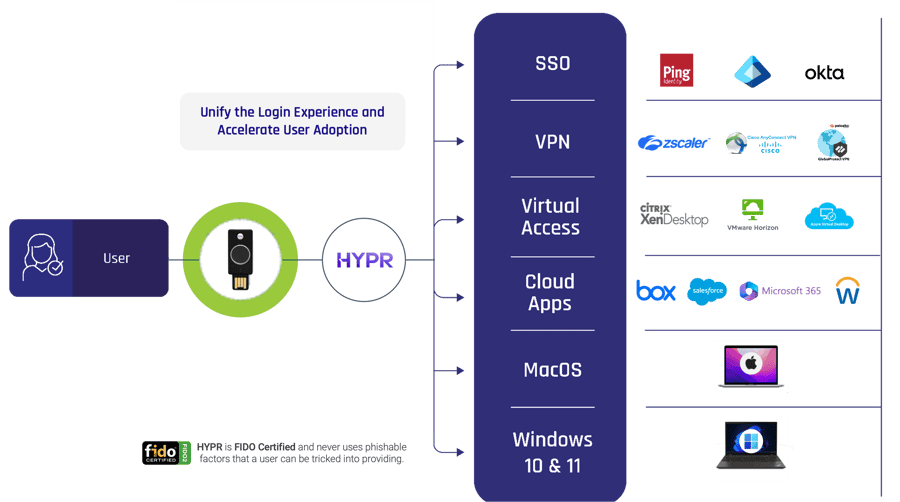
Implement YubiKeys with HYPR to better address compliance and security policies. HYPR gives you the flexibility you need to execute a comprehensive passwordless strategy across the enterprise whether it’s for single sign-on or desktop MFA.
Stop Identity Threats With Fast, Flexible, Authentication
- Eliminate Credential-Based Attacks: Combat man-in-the-middle, credential stuffing, phishing, and push bombing attacks with FIDO and smart card-based MFA.
- Log In Instantly: Get fast, convenient authentication using secure biometrics.
- Improve User Experience: Provide choice and flexibility, streamline login flows and reduce security fatigue.
- Ensure Compliance: Align with regulations and best practices with a mix of virtual and physical tokens, including PIV-compliant authentication.
Simplify Provisioning and Management
- Enable Easy, Self-Service Provisioning: No need to ship pre-provisioned YubiKeys or perform labor-intensive enrollment.
- Streamline Administration and Control: Use a single, powerful console to provision and manage both YubiKeys and HYPR virtual tokens.
- Cover all Environments and Use Cases: Create a seamless and secure login experience across all major IdPs and SSOs, for diverse environments and devices including Windows, MacOS, Linux, and VDI workstations.
Secure the Full Identity Lifecycle
Integrate HYPR’s Identity Assurance Platform, the most comprehensive end-to-end identity security for your workforce.
- Secure Identities From Day 0: Tie real world identity to digital credentials by uniting identity verification with provisioning workflows.
- Enforce Risk-Based Decisioning: Trigger re-authentication, or identity re-verification, based on cybersecurity ecosystem risk signals.
Supports Web-Based Authentication
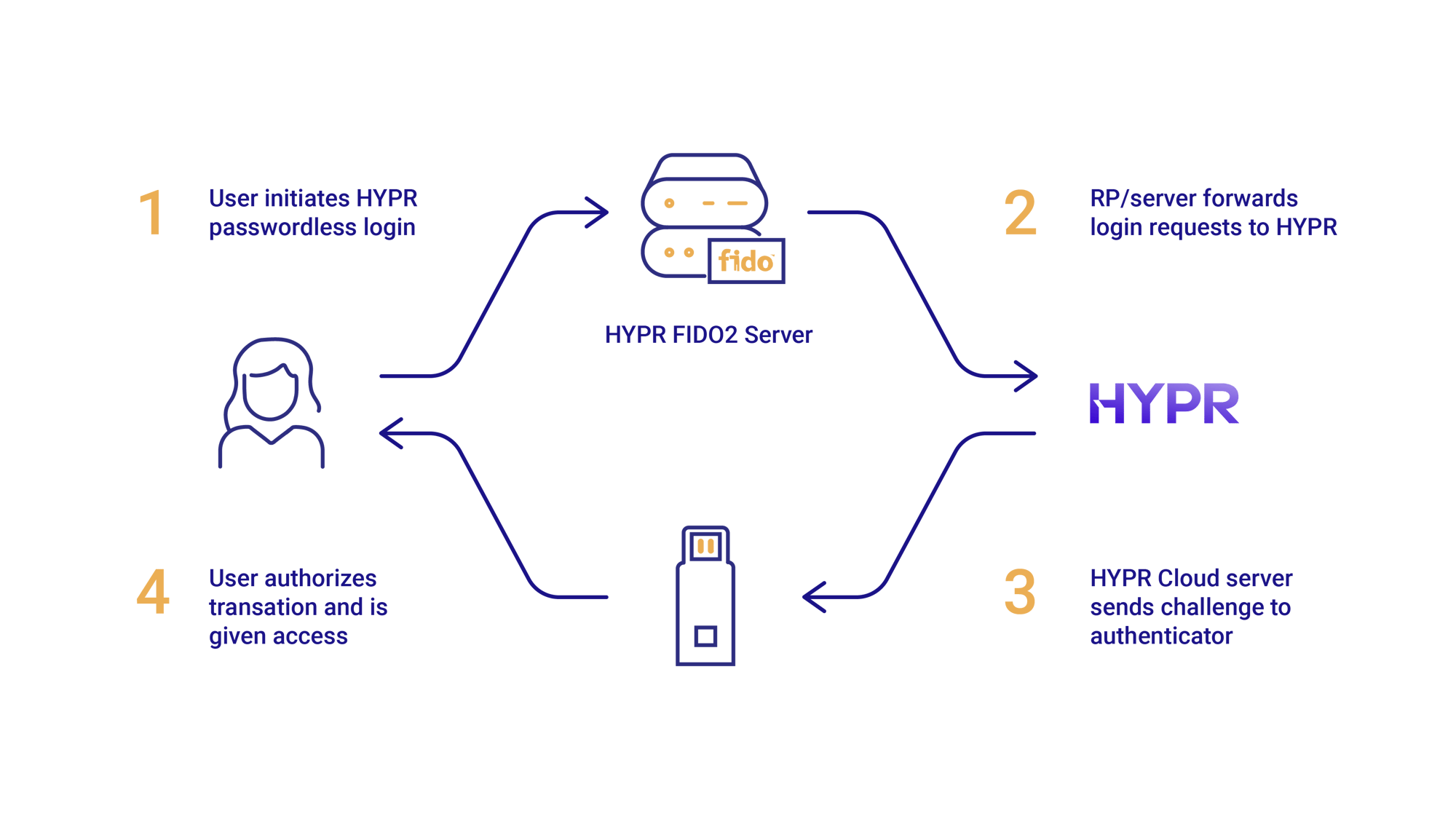
…and Workstation Authentication
Powerful Passwordless Authentication for YubiKey
Combine the YubiKey with your HYPR deployment for a powerful passwordless authentication solution that addresses the diverse needs of your organizations and users. Research shows that organizations using passwordless technologies experience the fewest phishing attacks, are more productive and achieve greater levels of employee satisfaction.
Use Cases for Hardware-Based Authentication
Ideal for situations where end-users are restricted from, or prefer not to use, smartphones for authentication. This includes organizations that require PIV-compliant authentication, call centers where mobile phones are prohibited, console users in banking, retail, and hospitality, or unionized workers without company-provided devices. Hardware tokens also offer a dependable backup and recovery option for mobile-based authentication.


Use Cases for Software-Based Authentication
Organizations can choose phishing-resistant, software-based authentication that uses mobile interactions people are already familiar with. Smartphone-based virtual FIDO tokens eliminate the need to buy and provision physical tokens for individual users, simplifying the enrollment process. They’re also highly convenient as people typically keep their phone with them.
Secure
Secure biometric and PIN-based passwordless login
Simple
Frictionless across devices and platforms to increase user adoption
Scalable
Quickly deploy at scale with HYPR’s easy, self-service provisioning

It's increasingly clear that passwords must go, which is why our collaboration with HYPR is an exciting one. Together, we can help businesses across the globe reach their journey to passwordless authentication with a joint solution that not only heightens security by eliminating password-based logins, but also accelerates productivity.
Derek Hanson
VP Solutions Architecture and Alliances, Yubico
Frequently Asked Questions
By combining physical and virtual tokens, the joint solution between HYPR and Yubico ensures secure and consistent user experiences, enables organizations to meet compliance requirements, reduces risks, and improves operational efficiency. By integrating Yubico and HYPR technologies, companies can:
-
Strengthen security posture across all use cases with FIDO and smart card-based MFA
- Prevent man-in-the-middle attacks, credential theft, phishing attempts, and push bombing attacks
- Create a seamless and secure login experience across diverse operating systems and devices, such as Windows, MacOS, Linux, and VDI workstations
- Work agnostically with all major Identity Providers (IdPs), Identity and Access Management (IAM) systems, and single signon (SSO) services
- Implement a strong authentication solution without being locked into a specific product suite or platform, allowing for greater flexibility and choice
- Align with regulations and best practices, with a mix of virtual and physical tokens, including PIV-compliant authentication
- Reduce costs associated with login resets, password fatigue, help desk calls, and employee downtime due to authentication issues
HYPR turns YubiKey onboarding into a self-service experience. End users pair their security keys, automatically enroll X.509 certificates, and enjoy seamless certificate renewals with no routine IT involvement required. This is done through:
- Admin Visibility: HYPR’s Console Integration gives administrators a consolidated dashboard of every YubiKey enrollment, certificate status, and recent identity verification events.
- Graceful Deprovisioning: HYPR enables endpoint-driven deprovisioning, where users retire lost or retired security keys directly from their workstation, ensuring true on-device certificate removal when possible.
- Resilient Multi-Factor Backup: Users can register multiple authentication methods or authenticator apps as primary and backup.
Achieving true end-to-end security requires a strategy that extends beyond the initial implementation of phishing-resistant authentication methods and provisioning of physical security keys. When deploying physical hardware authenticators, organizations can encounter significant operational complexities:
- Identity verification for onboarding: Before a YubiKey is issued (in person or shipped), organizations must be certain of the recipient's identity
- Loss, theft, damage, and lockouts: Physical security keys can be lost, stolen, damaged, or locked due to too many failed PIN attempts, which requires a secure recovery process
- Phishable fallbacks: In the case of a lost YubiKey, reverting back to easily phished methods like SMS/voice OTPs, email links, or security questions for recovery completely undermines the security gains
- Verified Recovery: Truly secure systems require a recovery process that incorporates strong, multi-factor identity verification
You can read more about the challenges with managing hardware security keys here.
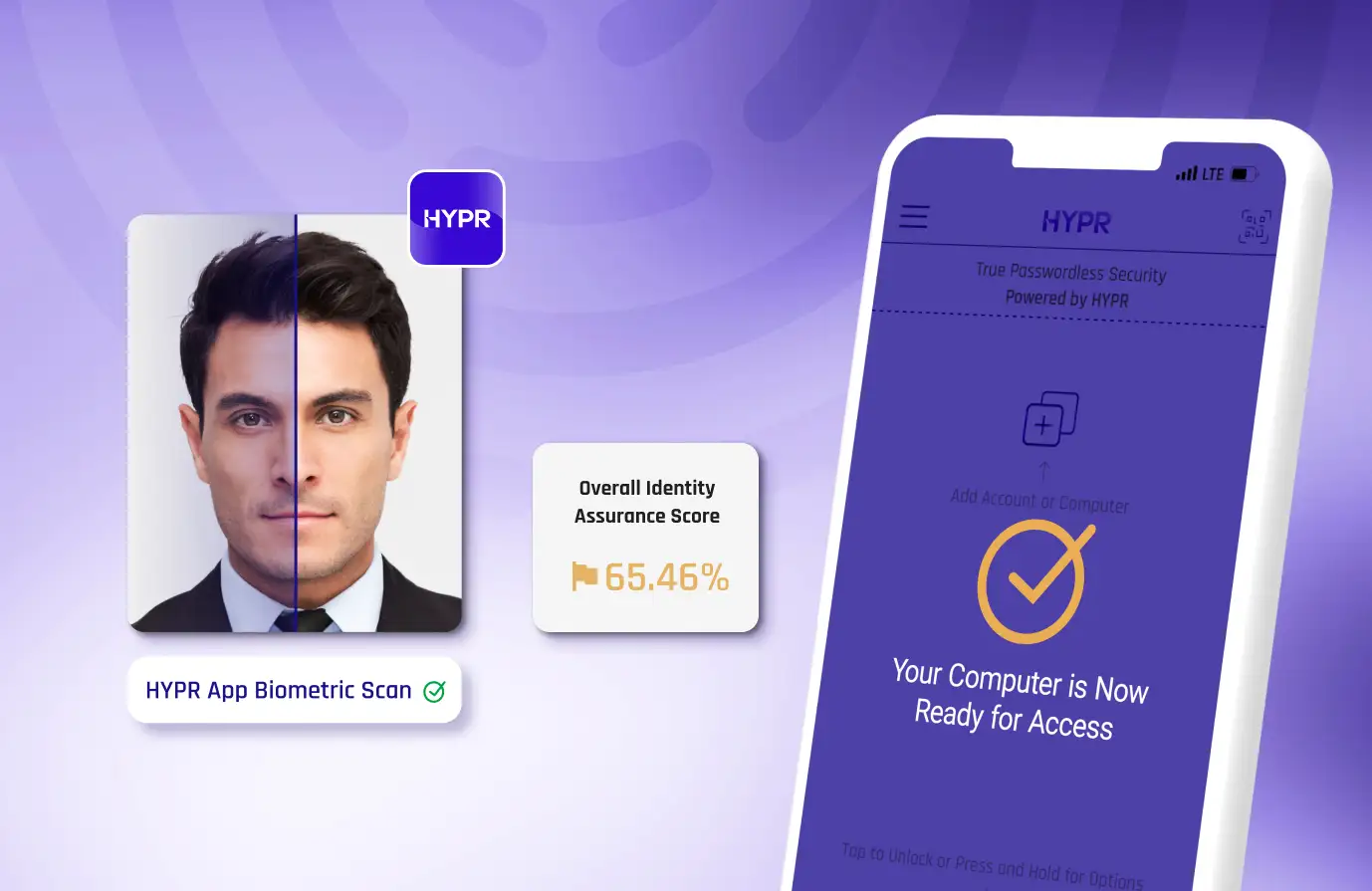
HYPR’s customizable Identity Verification (IDV) integrates directly into your onboarding flow before YubiKeys are provisioned. This process securely binds the verified physical identity to the digital identity and the associated credentials. It drastically reduces the risk of unauthorized access and establishes a trusted foundation for the user's entire lifecycle. HYPR offers a number of verification methods to align with your organization's risk tolerance:
- Device checks: HYPR first checks the device the user is verifying on to ensure it is the expected device.
- Location detection: A geolocation detection is performed and compared against expected location
- Documentation verification: Users are prompted to scan a government-issued ID (driver's license, passport), which HYPR analyzes for authenticity
- Biometric authentication: HYPR uses biometric data and facial recognition to ensure the person presenting the ID is its rightful owner
- Manager attestation: Combine live video verification and a secure chat with supervisors or IT to add an extra layer of assurance
HYPR eliminates this vulnerability by ensuring recovery processes maintain the same high level of security as primary authentication. If a user loses their YubiKey and needs to recover access, they leverage other already registered and verified strong authentication factors managed by HYPR.
Request a Demo
Experience passwordless MFA that secures and empowers your business. See what identity verification built for the workforce looks like. Learn how comprehensive Identity Assurance protects the entire identity lifecycle.
Fill out the form to get a demo from an identity security expert, customized around your organization’s environment and needs.




