Five Things to Know about the Crimeware Turned Cyberwarfare Tool
On December 23, 2015, just ahead of the busy Christmas holiday, 225,000 Ukrainians lost electricity under suspicious circumstances. The power outage lasted six hours, and it was later learned the shutdown was a deliberate, coordinated cyberattack to instill fear into Ukraine by hackers with close ties to the Russian government. (Since February 2014 the two countries had been in a protracted conflict over the status of the Crimea and Donbass regions.) An examination into the attack gleaned some surprising details. It was obvious that a strain of cheap malware had been deployed — but it had bespoke capabilities and it was used against critical infrastructure. The attack was orchestrated too carefully and intelligently over time to be mischief.
What is BlackEnergy? How was it used against Ukraine? Who is thought to be responsible? Here are five things you should know about BlackEnergy, the crimeware turned cyberwarfare tool.
1. BlackEnergy 1.0 is downmarket malware used for financial crime.
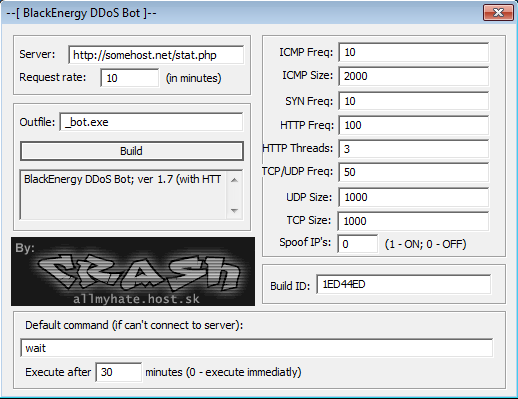
BlackEnergy dates back to 2007 as a rudimentary, off-the-shelf piece of crimeware used for theft and for distributed denial of service (DDoS) attacks. It was designed to infect Russian financial institutions’s website, spread throughout a network, and extricate financial information that would later be used for fraudulent purposes. The malware was known for its simplicity: it contained a graphical user interface and it was accompanied by a “For Dummies”-style help file. Despite the fact that an enhanced BlackEnergy file had been used against Ukraine in the December 2015 attack, the malware’s modest origins remain a source of irony. For around $40, any script kiddie could have obtained the foundational toolkit that caused a massive power outage tied to a bilateral conflict.
2. BlackEnergy 1.0 was succeeded by a nastier version that was customized for use against Ukraine.
In 2010, BlackEnergy received a major update, and it was during this time that BlackEnergy2 as it was known became interesting. Standing out was the added feature of modularity — support for the addition of various modules or plugins. These could be loaded as the attack ensued, for example while the main attack of financial data exfiltration was occuring the attacker could DDoS the same target's website to distract from the data removal. (There is also a BlackEnergy3, which was stripped down to its original intent.) The plugin support was what allowed attackers to gain the access and cause damage on the scale that it did, and beyond the potential of BlackEnergy 1.0, which was mere crimeware. An examination of BlackEnergy2 plugins yielded this functionality:
— A plugin called KillDisk (Win32/KillDisk) that overwrites more than 4,000 file types with random data and damages the OS by rendering it unbootable. A year prior, Kaspersky Lab had identified more than 20 Windows and Linux plugins in BlackEnergy, including a Windows file overwriter-destroyer (“dstr”).
— The KillDisk plugin version used against Ukrainian power companies restricted bootability but was also designed to sabotage industrial control system (ICS) software. Among the services it targeted were SEM Ubiquity, a kind of ICS software used at energy providers. KillDisk would overwrite data that would otherwise regulate and report on machinery in place.
The security firm ESET, which had monitored the attack on Ukraine, was the first to conclude that in addition to using the plugin-enriched BlackEnergy, the version used in the attack exploited an SSH backdoor (Win32/SSHBearDoor.A trojan). This allowed them at-will access to the target system, as outlined below.
3. BlackEnergy attackers used social engineering attacks on their targets.
While it came to light as the lights went out in late December of 2015, the BlackEnergy attack on Ukrainian utilities began much earlier. It started as spear phishing, with attackers targeting sysadmins for corporate account takeover (CATO). The adversaries posed as vendors and government officials, sending Microsoft Office attachments such as Word documents and Excel spreadsheets that contained the malware. Hackers installed KillDisk and gained persistent remote access. Once inside the network they guessed and stole credentials, moving through the enterprise laterally, creating backdoors. By way of other plugins the attackers also were infecting and remotely accessing ICS systems at the command and field levels, in some cases wiping endpoints and servers. The attackers also obtained virtual private network (VPN) credentials, which enabled them to observe the targets for weeks to better understand the systems and what they were breaking.
4. BlackEnergy attackers targeted industrial control systems (ICS) to inflict real-world damage.
As mentioned, BlackEnergy contained supervisory control and data acquisition (SCADA) plugins, enabling it to inflict physical damage at large enterprises, chiefly critical infrastructure in three categories: (1) Ukrainian ICS, energy, public sector and media, (2) global ICS/SCADA enterprises, and (3) the global energy sector. In this coordinated attack, the attackers overtook control of systems that regulated the function, monitoring, safety, and backups of (most often) major electricity providers. For example, they disabled an uninterruptible power supply (UPS) and disrupted communications by running illegitimate firmware updates. It was similar to the June 2010 novel Stuxnet, which ushered in a new kind of cyber warfare targeting the internet of things (IoT).
5. The BlackEnergy attack on Ukraine is believed to have been perpetrated by Russia.
In the hands of the right people, the existence of a late-version BlackEnergy is an advanced persistent threat (APT). Thanks to ESET, Kaspersky, and others, certain information is known due to BlackEnergy’s version profile (e.g. plugins’ targeting). Information such as the Windows backdoor, Windows files destruction, the ISC corruption all speak to the attack’s apparent motive and target. The use of BlackEnergy for the lengthy surveilling of Ukrainian energy providers as well as further expert examination of the attack have led the security industry to conclude that the attack on Ukraine was perpetrated by Sandworm. Known by several other names, Sandworm is a sophisticated, well-resourced hacking organization that has close ties to the Russian government, which is by no means a secret Ukraine’s #1 adversary. History would further show Sandworm doing Russia’s bidding. For one, Sandworm was implicated in the June 2017 global NotPetya attack that affected Maersk’s global supply chain and caused an estimated $10 billion dollars worth of damage.
That;s five things you now know about BlackEnergy. To learn more, read the Vice piece on BlackEnergy versions 1-3 and the Security Week postmortem on the BlackEnergy version behind the Ukraine takedown.
