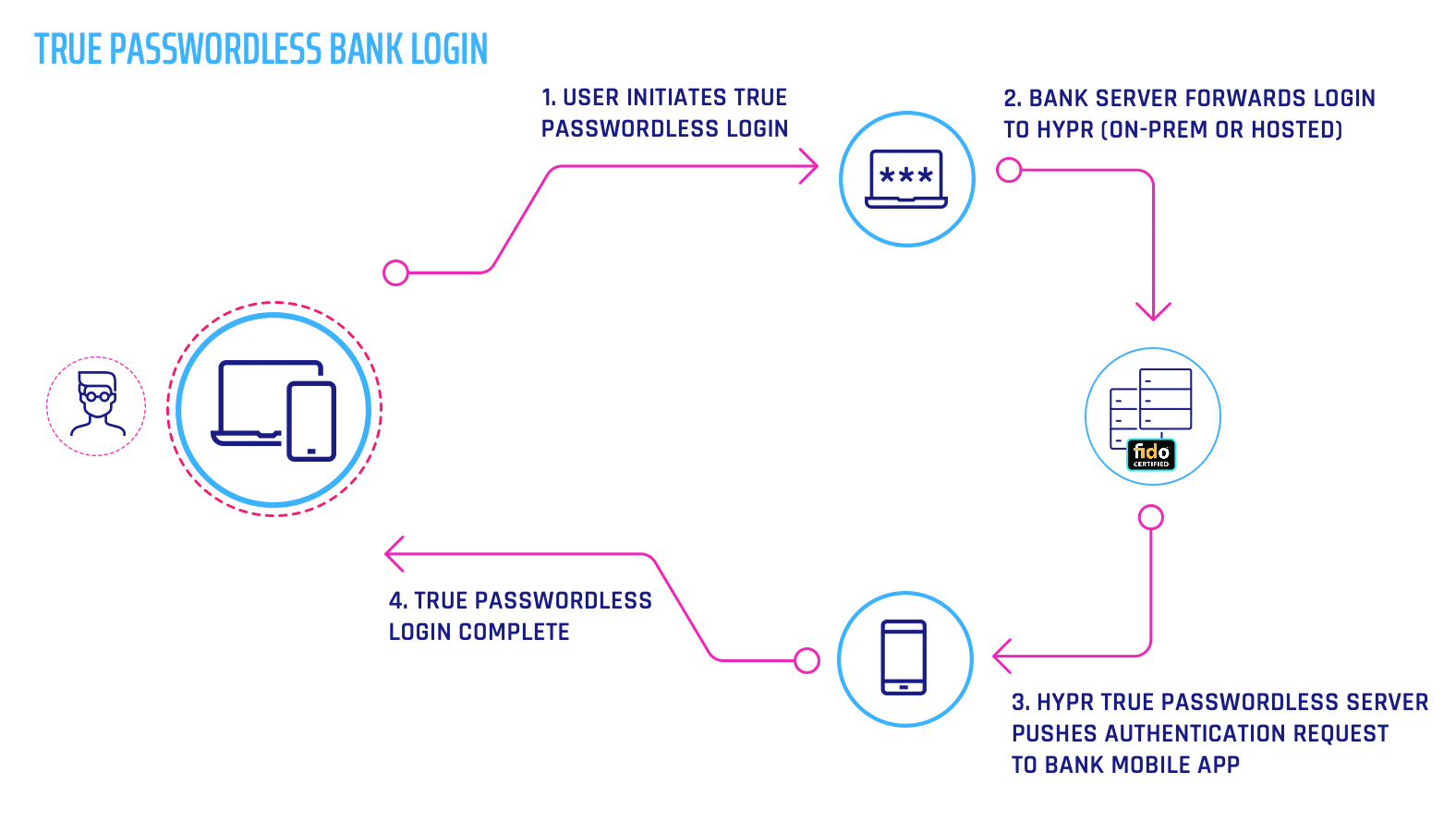
Push authentication is a mobile-centric authentication whereby the service provider sends the user a notification over the most secure available communication channel. The user responds to the challenge by performing an action to verify their identity and access the service. Push authentication relies on device possession as the dominant factor.
It often is deployed as part of a multi-factor authentication (MFA) solution with additional factors such as knowledge using a device PIN or decentralized PIN, or inherence using biometrics. Push authentication can be layered on top of a legacy centralized password regime (shared secrets) or it may be used as part of a passwordless system such as in a solution based upon FIDO architecture (true secrets).
PUSH notifications have also been the subject of recent attacks, with malicious hackers targeting users who may unwittingly approve a PUSH notification prompt for a transaction or login request. Learn more about PUSH Attacks.
Example:
"My insurance provider just enabled push-based authentication on my iPhone. Now instead of using passwords to log into the website, I just use a push notification on my phone to approve my login."
Push Authentication Demo:
Image: