A certificate authority (CA) is a trusted third party whose products help prevent man-in-the-middle (MITM) attacks between a user and an online service. The most common CA use case is for HTTPS to prevent MITM attacks against users while they are browsing websites.
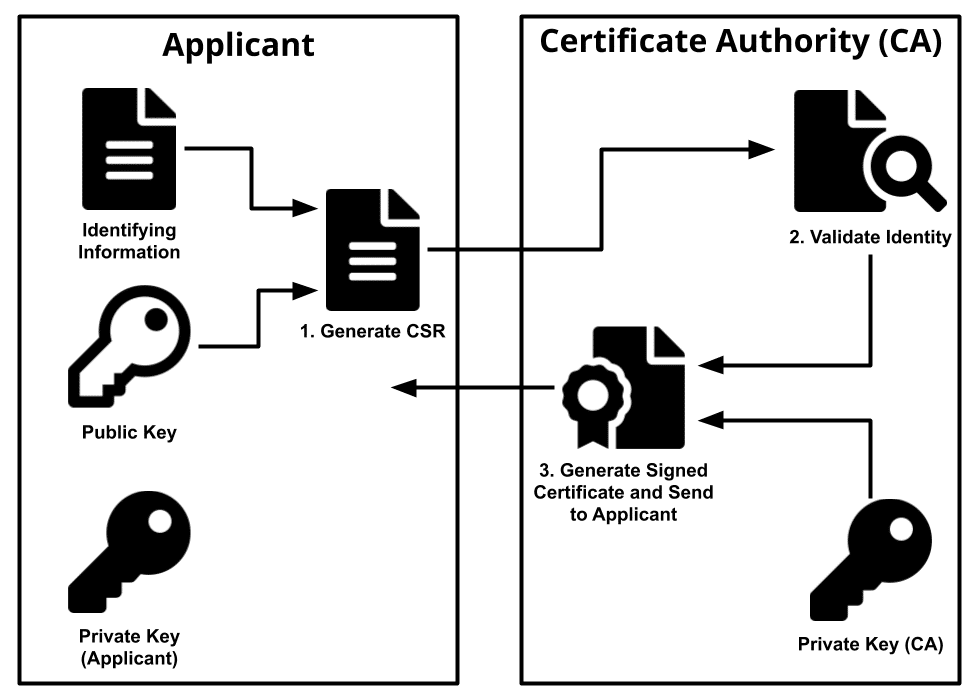
CAs are part of public key infrastructure (PKI). Users authenticate to the CA prior to connecting to the service to ensure they are establishing a secure connection between the intended parties. The client uses the CA certificate to authenticate the CA signature on the server certificate, as part of the authorizations before launching a secure connection.
Because the two intended parties are part of a closed loop, with the user’s (assumedly trusted) client-side software performing a challenge-response key exchange with the valid service’s keys, the MITM attacker is kept at bay as they are not party to the exchange.
Example:
"The Certificate Authority for our application is undergoing an acquisition by a foreign company. This is a very sensitive layer of security so we may consider terminating their service and using a different provider."
Image: