Solutions Authentication Built for PSD2 Compliance
Passkey-Based Authentication
Built for PSD2 Compliance
Comply with PSD2 SCA and Improve Customer Experience
Meet PSD2 Strong Customer Authentication requirements with secure, frictionless authentication that leverages FIDO Certified passkeys.
Fast, Simple Customer Experience
Protect Against Fraud and Cyberattacks
Reduce Costs and Increase Revenue
PSD2 SCA Challenges
Companies that don’t comply with PSD2 Strong Customer Authentication will have transactions denied and face penalties and fines, but compliance can create significant issues for businesses, including:
- Abandoned transactions and increased customer friction
- Increased costs related to integration costs, password reset costs, per-transaction SMS charges and other operational tolls
- Cyberattacks that bypass OTP and push-based MFA
- Compliance risks if methods do not conform to data residency and privacy requirements of regulations such as GDPR
Accelerate PSD2 SCA Compliance and Your Business
Achieve Strong Customer Authentication (SCA) for PSD2 while giving your customers a login experience that positively impacts customer satisfaction. With HYPR, you can meet evolving requirements quickly, at a lower cost, and with reduced strain on security resources.
Comply With PSD2 Authentication Requirements and More
Easily meet PSD2 SCA regulatory technical standards (RTS) with:
- Strong passkey-based multi-factor authentication that uses independent inherence and possession factors
- Support for dynamic linking
- Secure, separated execution environment
- Risk-based, step-up authentication
- Satisfies data residency and privacy requirements and aligns with Zero Trust, MITRE, PCI DSS requirements, and other standards

Strengthen Authentication Security
- Replace passwords and legacy MFA with a secure passkey ecosystem
- Stop credential phishing, ATO, MitM, MFA bombing and other credential attacks and breaches
- Prevent fraudulent transactions with adaptive authentication that continuously monitors for increased risks
- Build customer trust with secure, cutting-edge authentication
Eliminate Customer Friction
HYPR makes authentication easier and faster.
- Simplify MFA login to a single user action for login that’s 3x faster than legacy methods
- Support customer choice with a variety of FIDO authentication options
- Unify siloed identity systems
- Ensure a consistent user experience across different devices and platforms

Integrate and Deploy Passkeys Quickly
- Accelerate development with an easy to use SDK
- Rapidly build passkey support into apps with HYPR FIDO2 API and servers
- Integrate with your current systems, IdPs and applications to unify authentication across the business
- Rely on the experts in CIAM passkey deployments
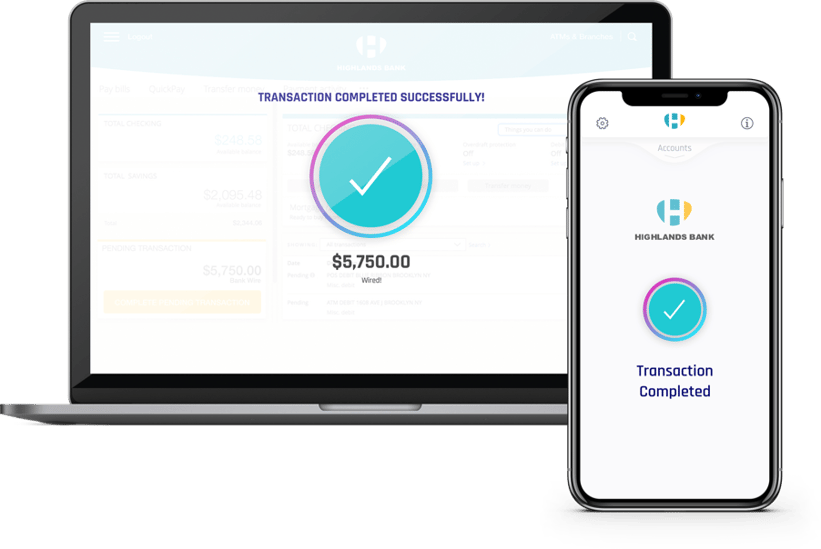
How Does It Work?
At the time of registration a user’s private key is generated from a biometric such as a fingerprint or face. HYPR ensures this passkey always remains on their personal device and is used to sign transactions, including the transaction amount, payee ID and other data.
Once a transaction is processed, HYPR responds with a signed response that cryptographically links this data to the authentication code required by SCA, fulfilling the “dynamic linking” requirement for transactions processed on mobile and web applications.

Customers Using HYPR for Their Customers
 HYPR's passwordless authentication SDK provides a strong alternative to phishable and inconvenient passwords — and it works across devices customers use in their daily lives already.Arshal AmeenGlobal Head Application Development, Rakuten
HYPR's passwordless authentication SDK provides a strong alternative to phishable and inconvenient passwords — and it works across devices customers use in their daily lives already.Arshal AmeenGlobal Head Application Development, Rakuten
 Just ten weeks into their HYPR passkeys rollout, this Fortune 50 Healthcare Corporation deployed passkeys to more than one million customers.Learn MoreIT Director
Just ten weeks into their HYPR passkeys rollout, this Fortune 50 Healthcare Corporation deployed passkeys to more than one million customers.Learn MoreIT Director
 True Passwordless Security provides not only an ability for me to help drive a strategic vision that addresses security and fraud risk for my enterprise, it also helps me drive a vision, meet the digital engagement goals, and provide users and our customers with a better experienceLearn MoreBrian HeemsothFormer Executive Director of Global Security, CVS Health
True Passwordless Security provides not only an ability for me to help drive a strategic vision that addresses security and fraud risk for my enterprise, it also helps me drive a vision, meet the digital engagement goals, and provide users and our customers with a better experienceLearn MoreBrian HeemsothFormer Executive Director of Global Security, CVS Health
 The ability to deliver strong passwordless authentication to our customer base is critical to our vision for a secure digital health experience. HYPR has empowered us to realize that vision at scale.Learn MoreDamien MullanIT Manager, Vhi Healthcare
The ability to deliver strong passwordless authentication to our customer base is critical to our vision for a secure digital health experience. HYPR has empowered us to realize that vision at scale.Learn MoreDamien MullanIT Manager, Vhi Healthcare
 HYPR's technology is a smart way to keep critical data where it belongs - close to the customer.Learn MoreExecutive Vice President, Mastercard
HYPR's technology is a smart way to keep critical data where it belongs - close to the customer.Learn MoreExecutive Vice President, Mastercard
Related Resources
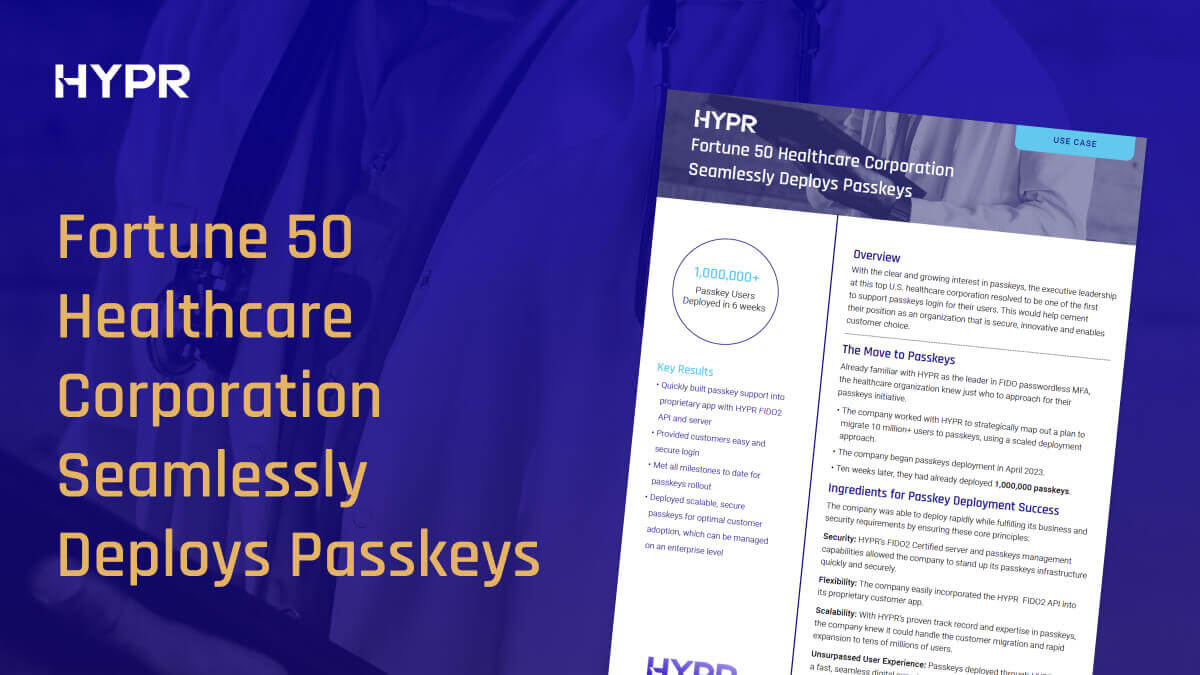
Fortune 50 Healthcare Corporation Deploys Passkeys
This healthcare corporation rolled out passkeys to over a million customers in 10 weeks.

Open Banking and Strong Customer Authentication
Learn about Open Banking and how to comply with SCA requirements.
HYPR Alignment With the MITRE ATT&CK Framework
Understand the MITRE ATT&CK categories and techniques on authentication attacks
An Intro to PSD2 SCA Requirements
What you need to know about the PSD2 Strong Customer Authentication requirements.
Request a Demo
Experience passwordless MFA that secures and empowers your business. See what identity verification built for the workforce looks like. Learn how comprehensive Identity Assurance protects the entire identity lifecycle.
Fill out the form to get a demo from an identity security expert, customized around your organization’s environment and needs.



