Introduction to Passwordless Authentication
As a general concept, passwordless authentication is straightforward — it’s a means of verifying a person’s identity without using a password. Instead it replaces them with more secure authentication factors like possession factors or biometrics. In its strongest forms, passwordless authentication solves one of the most persistent cybersecurity gaps today and can also make the login process faster. In fact, we found in our report The State of Passwordless Security 2023, that 86% of organizations believe passwordless authentication is essential to both the security and efficiency of their business.
In practice, the passwordless space is rapidly evolving, and the confusing terminology can make it difficult to understand what passwordless authentication is, the key principles and how it functions in the enterprise. Whether you’re a seasoned security veteran or just getting started, this guide aims to simplify passwordless technology. From how passwordless authentication works, to what to look for in a solution, this in-depth guide will help you get started on your journey toward becoming a truly password-free organization.
Why Are Passwords So Risky?
Passwords are inherently vulnerable because simple “username and password” combinations are easy to hack. Attackers can steal or guess passwords, and it doesn’t help that 64% of us re-use passwords across numerous accounts, so one hack equals instant access to multiple logins.
Some of the most common types of password attacks include:
-
Brute force attacks: This involves an attacker attempting numerous passwords or passphrases with the aim of eventually guessing the correct one. Using automated attacks tools, the attacker systematically tries all possible combinations of words, letters and characters until a match is found. The longer and more complicated the password, the longer it takes. Often they will use additional known data points, such as minimum password length or a requirement that it includes certain characters, to increase their chance of success.
-
Phishing: The practice of sending fraudulent emails, text messages, phone calls or spoofed websites, disguised as legitimate ones, designed to persuade users to download malware or divulge personal information, such as a password or credit card number. Login credentials are the top target of phishing scams. Generative IA tools allow attackers to generate phishing lures that are highly personalized and convincing.
- Adversary-in-the-middle (AitM) attacks:
Also known as a man-in-the-middle (MitM) attack, a perpetrator positions themself in a conversation between two parties — two users, two devices, or a user and an application or server — so that all communications are going to or through the attacker. Public WiFi is a popular vehicle for AitM. By breaching communiations, the attacker can steal any shared credentials, payment card details or other sensitive information.
-
Credential stuffing: This type of attack leverages username and password combinations stolen in previous database breaches. Since many people reuse their passwords across different accounts, the attacker uses automation tools to inject the stolen username and password pairs into login forms en masse.
-
Keylogging: Keystroke loggers capture keystroke information as a user types it in. They are often used in cyberattacks to steal sensitive information and credentials. When used maliciously, keyloggers are considered a type of spyware. However, keyloggers can also be used for legitimate purposes, such as troubleshooting issues on a device or monitoring children's computer use.
- SIM-swapping: Using personal information gathered through social engineering or other sources, the attacker convinces the victim's cell company to switch the phone number to a SIM card the attacker controls, usually by claiming the phone was lost or stolen. This means that attackers can use OTPs or account recovery information sent to that phone number to take over the victim’s accounts.
The best way to protect your organization against password-based attacks is by going passwordless. Fortunately, it’s much more feasible than you might think.
What Are the Different Authentication Factors?
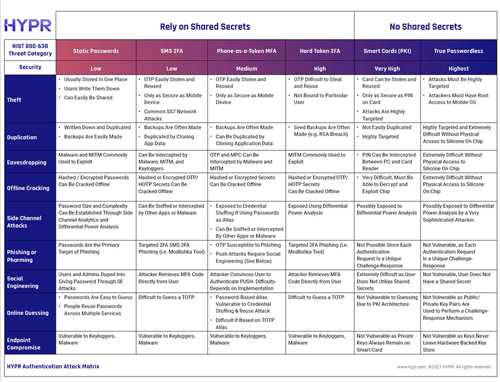
There are three different categories of authentication factors: knowledge, possession and inherence, and it’s important to understand the differences between them before you attempt to understand the concept of passwordless security.
- Knowledge: In this category, you have to prove who you are with “something you know,” like a password or secret question.
- Possession: In this category, you have to prove who you are with “something you have,” like a security key, device, or one-time password.
- Inherence: In this category, you have to prove who you are with “something you are,” like a biometric fingerprint or facial scan.
Two-factor authentication requires using two such factors. Multi-factor authentication (MFA) requires two or more independent factors, meaning from two different categories.
What is Passwordless Authentication?
Passwordless authentication removes shared secrets or knowledge as an acceptable factor in the authentication process, as this category is most easily hacked. Instead, it only allows possession or inherence authentication factors. While it is possible for passwordless to be single-factor (ex: hardware security key), most passwordless solutions are multi-factor.
While passwordless should, in theory, mean authentication is free from passwords, some solutions provide a passwordless experience but still actually use passwords at some point in the process. For example, the user may verify their identity with biometrics on the front end, which is linked to a password that gets transmitted to a server on the back end.
Fully passwordless authentication solutions completely remove knowledge factors and shared secrets from authentication, and do not transmit or centrally store secret credentials.
How Does Passwordless Authentication Work?
The goal of “gold standard” true passwordless authentication, namely the Fast Identity Online (FIDO) specifications, is to completely remove shared secrets from the authentication process. Under FIDO and the expanded FIDO2 standards, authentication between the user and server is done through public key cryptography.
Here’s how a typical passwordless login flow works in practice:
Step 1: The user begins the login process, which sends an authentication request to the server.
Step 2: The authentication system challenges them to provide the required factors.
Step 3: A secure local action on the user's device, such as providing a face scan or thumbprint or using a security key, will unlock the private key.
Step 4: The private key is used to sign the challenge, proving user possession.
Step 5: The authenticating server verifies that the signature matches the stored public key.
Step 6: Upon a successful match, the user is authenticated for entry to the system.
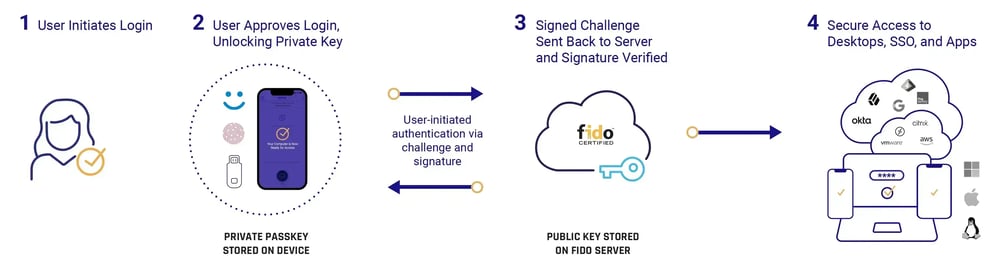
In short, a user’s biometric features (inherence) unlock a private key on their device (possession) through an authenticator. Using cryptographic exchange protocols, this private key is matched with the public key of the partnership, verifying the user’s identity without sharing secrets or needing server-side databases.
Common Passwordless Login Methods
There are multiple password-free authentication methods, some relying on software, some on hardware. As mentioned earlier however, some solutions provide login methods that seem to be passwordless but actually use some form of shared secret and therefore can be breached, hacked or intercepted. One-time passwords (OTPs), magic links and even some biometric authentication methods fall under this category and technically are not passwordless.
Common passwordless authentication methods include:
- Push authentication (this may or may not be phishing-resistant depending on the implementation)
- Biometric FIDO/FIDO2 Authenticators
- Passkeys
- Hardware security keys
- Windows Hello Passwordless
- Smart cards (PIV)
Of course if any of these are used in combination with a password as a factor, then they are no longer passwordless.
The Pros and Cons of Passwordless Authentication
Passwordless authentication eliminates many of the challenges associated with legacy authentication methods. However, like any technology, it has pros and cons. Consider each when deciding if moving to passwordless technology is right for your organization.
The Benefits of Passwordless Authentication Solutions
Passwordless has several unique benefits over other types of authentication, including:
- Enhanced security: Passwords are the root cause of most cyberattacks; per Microsoft, there are over 18 billion password attacks a year. Getting rid of passwords drastically lowers your authentication risk profile.
- Improved user experience: Forgetting passwords and going through password resets are major sources of user frustration. Modern passwordless solutions can securely authenticate a user in seconds with something they almost always have in their possession (a personal device or biometric feature).
- Reduced IT costs: Password-based systems place a heavy burden on security teams, who must set and inform users about policies, ensure high levels of security around storage, and manage resets. The costs are significant, with password resets and other password-related issues costing companies an average of $375 per employee annually.
- Increased productivity: Login processes, including failed attempts, trying to remember a password, and resetting passwords, take up an average of three working days per employee. Simplifying the process with a passwordless solution improves access times, condensing multiple steps into a single action.
The Drawbacks to Passwordless Authentication Solutions
As with any technology and any significant change, passwordless authentication can bring potential challenges. These will vary depending on the type of passwordless solution and the organization’s IAM and IT environment. Areas to consider include:
- Costs: Passwordless authentication that relies on hardware security keys introduces costs for the security keys and their ongoing management. Passwordless solutions that use mobile authenticators may require upgrading employee devices for those who do not possess smartphones.
- Expertise: Many IT teams have years of experience troubleshooting password-based systems, which are relatively straightforward.
- Change Management and Delayed Adoption: Despite being a source of frustration, most people are comfortable with passwords. While passwordless authentication is more convenient in many ways, most people are not yet familiar with it. They will need time to transition to a new method of authentication. Making sure your passwordless methods are easy to use and employing a clear change management strategy will increase adoption rates.
Passkeys and Passwordless Authentication
Passkeys are a phishing-resistant replacement for passwords developed by the FIDO Alliance. There are two primary types: synced and device-bound. Synced passkeys can be used on multiple devices without re-enrolling each device. Since 2022, Apple, Google, and Microsoft have been rolling out support for synced passkeys across their various OSes.
On an enterprise level, device-bound passkeys are generally preferable as they can include features and controls that consumer passkeys do not. The HYPR authenticator is an example of a FIDO device-bound passkey that can be used for desktop access and integrates with the enterprise's overall technology stack.
Passwordless Security, Passkeys and Zero Trust
The cornerstone of any Zero Trust security initiative is passwordless phishing-resistant multi-factor authentication as defined by the OMB, CISA and other security frameworks.
By using FIDO device-bound passkey security standards, organizations can institute Zero Trust authentication principles without adding friction to the user experience. It establishes the required trust of the user's identity, ensuring that your authentication processes align with the highest level of assurance (NIST 800-63B AAL3) and creating a solid foundation for your Zero Trust security architecture.
Note that synced passkeys do not provide this same level of assurance. Moreover, organizations will need to make sure they address all use cases, such as dispersed workforces, remote employees or those traveling often.
What To Look For in a Passwordless Solution
Not all passwordless solutions are equal, and many don’t offer the same levels of security. Furthermore, some solutions aren’t even “true” passwordless; these subpar solutions remove the shared secrets from the user’s view but still use them on the backend.
If you’re investigating passwordless authentication solutions, here’s a checklist of essential capabilities to look for:
✓ Completely removes shared secrets (passwords, OTPs), even for fallback flows
✓ Provides phishing-resistant desktop login as well as web apps
✓ Declutters the user experience and reduces login friction
✓ Uses the hardware Trusted Platform Module (TPM) or Secure Enclave to store private keys and other sensitive data
✓ Easy to deploy for IT teams
✓ Supports secure authentication for remote workers and works offline
✓ Integrates with major identity providers (IdPs) and devices
✓ Intuitive for users to learn and adapt to
✓ FIDO Certified for all components
✓ Achieves compliance with Zero Trust architecture and regulatory obligations
✓ Reduces the overall total cost of ownership (TCO) for authentication security
Passwordless Security Evaluation Guide
Organizations across all sizes and sectors are looking to passwordless technologies to make their authentication processes more secure while reducing friction.
This guide will help you assess passwordless security products and determine which solution best suits the needs and requirements of your organization.
HYPR Passwordless Authentication
HYPR's passwordless authentication solution meets all your requirements. It turns an ordinary smartphone or other device into a PKI-backed security key for frictionless, phishing-resistant login from desktop to cloud.
HYPR Workforce Access: Empower your employees and business with easy-to-use, passkey-based authentication. Secure your workforce with phishing-resistant MFA and adaptive risk management that deploy rapidly into your existing infrastructure.
HYPR Customer Authentication: Reduce customer frustration while protecting against account takeover and fraud. HYPR's passkey-based MFA and proactive risk controls remove friction and ensures you meet strong customer authentication requirements (SCA).
Passwordless FAQs
Yes. Passwords are the greatest threat to authentication security, and credential-related attacks are the biggest cyberattack vector. Unlike traditional MFA, passwordless MFA does not allow the use of passwords or other shared secrets to log in, making it a much safer solution.
The safest authentication method is the one that’s most difficult for attackers to bypass. Passwordless solutions such as biometric identifiers or unique key cards would require a dedicated attempt to acquire those specific details, which costs far more time and money than most attackers are willing to spend.
Yes. Google is rolling out Passkeys, a passwordless authentication solution, across its Chrome and Android operating systems.
FIDO2 combines the specifications for the FIDO Alliance’s Client-to-Authenticator Protocol (CTAP) and the World Wide Web Consortium’s (WC3) Web Authentication (WebAuthn) specification. WebAuthn is a standard for authenticating users to web applications, allowing users to securely authenticate themselves without their information ever being passed to the website or application.
You’ve probably heard of multi-factor authentication (MFA), which shares some of the same objectives as passwordless authentication. There are, however, some distinct differences between passwordless and MFA. MFA allows users to verify their identity with any of three factors (knowledge, possession, inherence), whereas passwordless authentication generally only accepts possession and inherence factors (in some cases a local device PIN may be used in place of, or in addition to, a biometric).
Also, importantly, many passwordless solutions, especially those built on FIDO standards, have recognized user friction as a key source of security lapses. As such, most passwordless solutions have a strong “user friendliness” objective, which is absent from many MFA models.