Stop Insider Threats
Stop Identity Fraud and Improve Productivity With Passwordless Identity Assurance
Get a DemoLooking for the HYPR logo and visual assets? Check out our Media Kit.
Stop Identity Fraud and Improve Productivity With Passwordless Identity Assurance
Get a DemoThe identity verification solution that automates candidate and new hire screening - built for your HR team.

Achieve zero password reset calls with streamlined, automated account recovery.

The identity verification solution that automates candidate and new hire screening - built for your HR team.

Achieve zero password reset calls with streamlined, automated account recovery.

2 of the Top 4
U.S. Banks Trust HYPR0
Password Reset Calls55,000,000+
Deployed Users and Growing“The biggest benefit of working with HYPR is that they make things easier and more secure, as well as their unbelievably great support.”
Jörg Schlottbohm CISO, BOS FOOD"The single most important thing we can do is eliminate the human-targeted risks. HYPR’s approach is fundamental to that."
IAM Leader, Global 500 Bank"We needed to remove the security risks of remote hiring without adding friction. HYPR was the answer."
VP of People, Fortune 500 ManufacturerDrastically reduce the risk of data breaches by eliminating the primary attack vector; passwords. HYPR provides a quantifiable 324% ROI verified by Forrester, helping you justify security investments and secure your enterprise from end-to-end.
Discover Your ROIMitigate threats by ensuring every user is who they claim to be with phishing-resistant MFA and multi-factor identity verification. HYPR combines its own data with telemetry from security partners like CrowdStrike to help you make contextual access decisions and prevent unauthorized access to sensitive systems.
See It in ActionStop fake applicants and prevent interview fraud with automated identity verification. Ensure new hires are who they say they are and can securely access necessary systems from day 0 for a seamless and productive onboarding experience.
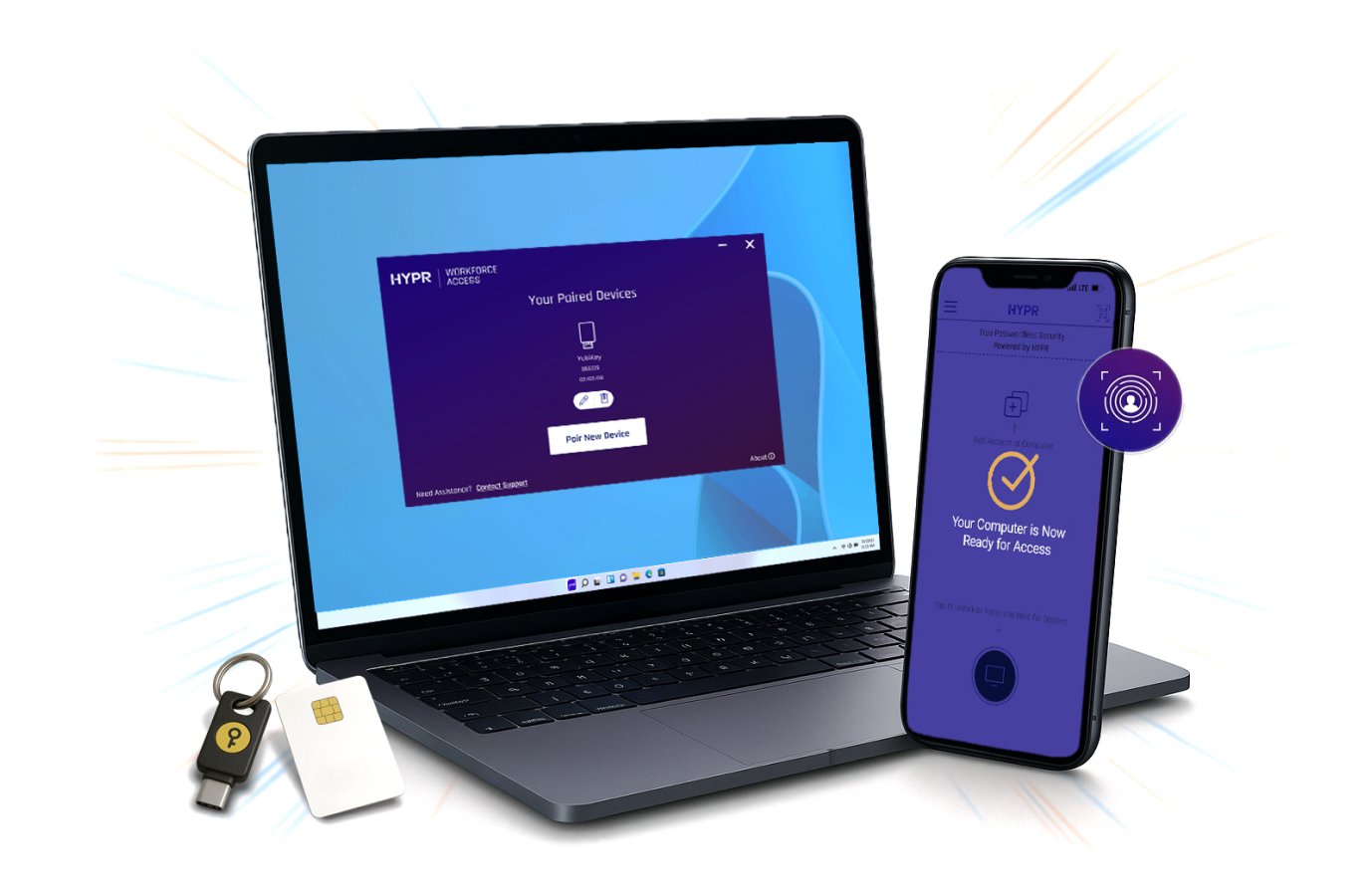
See How Identity Verification WorksEliminate passwords and integrate limitless phishing-resistant authentication flows for your unique environment.
Stop fake applicants and interview fraud with strong, automated identity verification.
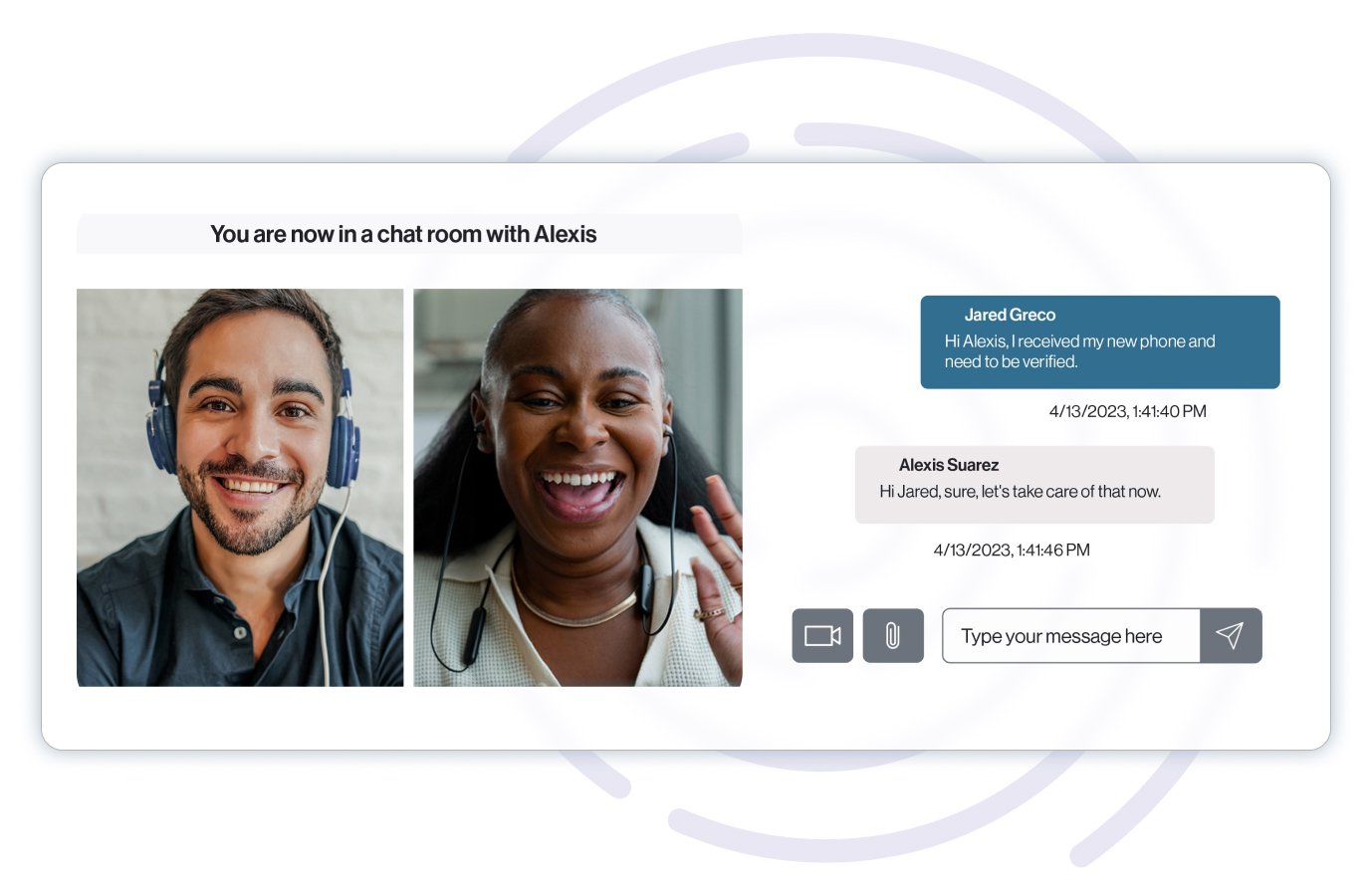
Stop social engineering and cut IT tickets by verifying users and enabling self-service MFA resets.


Phishing-resistant MFA from desktop to cloud built on proven open standards with no password-based fallbacks

End-to-end identity security from day zero with unified passwordless authentication, adaptive risk mitigation, and automated identity verification

Limitless authentication flows and continuous real-time risk assessment to deliver a world-class experience for all users

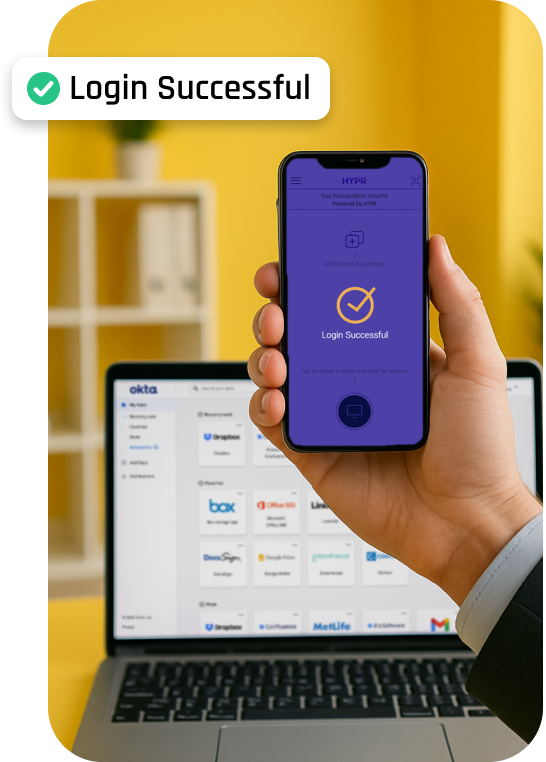
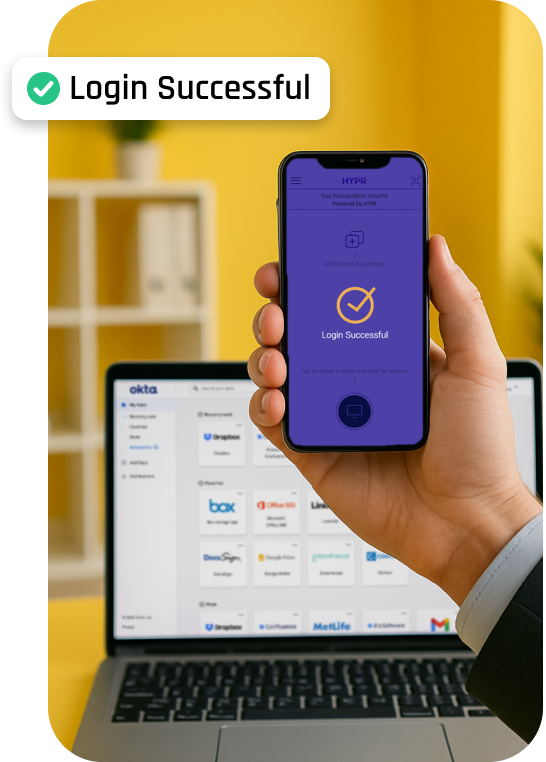
HYPR has made the login experience seamless for my team. It was quick and easy to set up for our Okta users, and I appreciate that we can configure it to allow users to log in once at the workstation level, then seamlessly access our SSO without needing additional authentication.


HYPR is easy to manage. My end users love using HYPR to login to their computers.


The multifactor solution for iPhone and Android is bar none for corporate environments. Users have one app for all their MFA. Integrates with all of our tools using SAML.


The team at HYPR goes above and beyond to make sure our deployment is successful. The focus on end user experience is key.


I like how HYPR works across multiple platforms seamlessly. I use it on a daily basis with my iPhone and work computer.


The Sixth Edition State of Passwordless Identity Assurance report offers organizational leaders and frontline IT personnel crucial insights into identity threats, technologies and trends, empowering them to steer through one of the most swiftly evolving and mission critical areas of IT and security.
.jpg)
Toward Converged Identity Assurance
Understand the drivers and guidelines for a converged Identity Assurance approach.

What Is Identity Assurance and Why It's Needed
Best practices for identity assurance in today's modern enterprise.
The Total Economic Impact
of HYPR
Forrester Consulting calculates that HYPR customers save millions, with a 324% ROI.