Platform HYPR + Okta Integration
Passwordless Authentication for Okta
Secure your Okta environment with the HYPR Identity Assurance Platform and experience the highest level of identity security.
HYPR introduces phishing-resistant, passwordless MFA to your Okta SSO, eliminating passwords and fortifying your defenses against account takeovers and unauthorized access.

Extend Your Investment in Okta
Through our close integration, HYPR’s native plugins enable passkey-based, phishing-resistant login for Okta environments including single sign-on, Desktop MFA and mobile-to-web authentication.
Unlock the Power of HYPR Passwordless Authentication:
- Interoperability with FIDO U2F security keys such as YubiKey, and built-in platform authenticators such as Windows Hello.
- Cross-cloud, cross-platform passwordless login to Windows, MacOS, Linux and VDI workstations.
- Full protection against man-in-the-middle (MitM), credential stuffing, phishing and push bombing attacks.
- Ease of deployment and use by admins and end users alike.
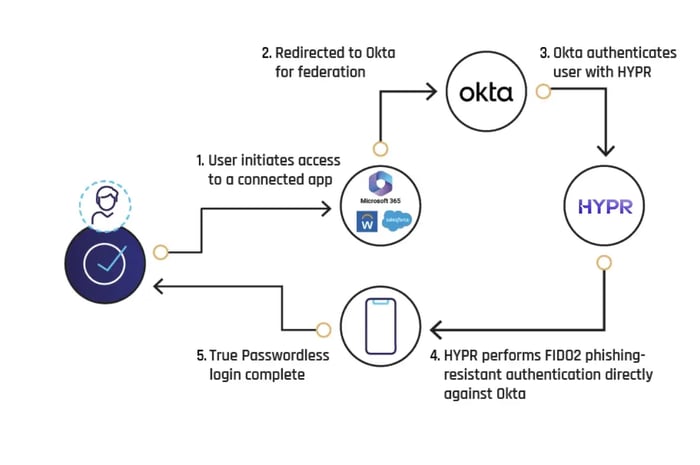
Secure, Single Action Login to Okta
Desktop SSO with HYPRspeed. From Okta, you authenticate once using HYPR to gain access to Okta and all downstream apps.
If you already signed into your desktop with HYPR, then the authenticated identity is automatically passed to Okta. No additional verification steps, unless step-up authentication is required.
Secure Identities from End to End
From Day Zero
- Reactive Risk Policy Engine: Push your security infrastructure further with a policy engine that integrates data from endpoints, browsers, and various security tools to deploy adaptive risk mitigation strategies, dynamically countering threats in real time.
- Integrated Identity Verification: From self-service all the way to manager video approval, our completely customizable identity verification processes guarantee access exclusively to authorized users.
Learn about the HYPR | CrowdStrike Integration.
Leading Companies Secure Their Identities With HYPR
-

HYPR has made the login experience seamless for my team. It was quick and easy to set up for our Okta users, and I appreciate that we can configure it to allow users to log in once at the workstation level, then seamlessly access our SSO without needing additional authentication.
IT User -
HYPR is easy to manage. My end users love using HYPR to login to their computers.
Shane C.Cybersecurity Administrator -
The multifactor solution for iPhone and Android is bar none for corporate environments. Users have one app for all their MFA. Integrates with all of our tools using SAML.
Manufacturing User -
The team at HYPR goes above and beyond to make sure our deployment is successful. The focus on end user experience is key.
Financial Services User -
I like how HYPR works across multiple platforms seamlessly. I use it on a daily basis with my iPhone and work computer.
Automotive User

Frequently Asked Questions
With HYPR's integration for Okta, you drastically reduce your attack surface while making login faster and simpler for your users. It turns an ordinary smartphone or other device into a FIDO Certified, PKI-backed security key for a frictionless, phishing-resistant login from desktop to cloud. The main benefits include:
- Separating your IdP from authentication: SSOs are effective services for easing workflows and managing access to a user's suite of applications; however, this places a significant target on its back for attackers seeking access to those user privileges. Separating the authentication providers from SSO providers and using a more secure passwordless authentication solution makes it more difficult for attackers to bypass.
- Implementing phishing-resistant passwordless MFA: One of the major Okta security issues is how easily attackers can phish, intercept or bypass MFA security that uses SMS, OTPs or push notification. By removing passwords and phishable factors, and authenticating using biometric identifiers and public key infrastructure (PKI), you eliminate the potential for phishing, MFA bombing and man-in-the-middle attacks.
- Protecting desktop login or offline users: Okta's more secure authentication methods do not easily extend to desktop login, VPN access or remote situations. With HYPR, you can ensure you have identity security processes in place to cover all use cases and user populations.
- Deploying continuous identity verification: HYPR utilizes multi-layered, risk-based identity verification that combines a series of factors such as location, behavior, document verification and face recognition so that you can be certain that an identity is genuine.
The other major risk associated with Okta's native authentication methods is that using an identity provider to log in to the same identity provider creates significant risk for access. Implementing a third-party, phishing-resistant, passwordless MFA solution like HYPR helps mitigate the centralized risk within your Okta environment by removing the authentication burden from the SSO.
Additionally, some of Okta's more secure authentication methods are not compatible with modern workforce arrangements: desktop logins, offline users, VPN access, or remote work scenarios. HYPR provides flexibility to ensure your authentication methods cover all of your use cases.
Related Resources
Passwordless Security Evaluation Guide
12 key considerations when choosing passwordless authentication.
Go Passwordless with Okta
Experience passwordless MFA that secures and empowers your business. See what identity verification built for the workforce looks like. Learn how comprehensive Identity Assurance protects the entire identity lifecycle.
Fill out the form to get a demo from an identity security expert, customized around your organization’s environment and needs.
Request a Demo
Experience passwordless MFA that secures and empowers your business. See what identity verification built for the workforce looks like. Learn how comprehensive Identity Assurance protects the entire identity lifecycle.
Fill out the form to get a demo from an identity security expert, customized around your organization’s environment and needs.