Stop Identity-Based Attacks Without Slowing Down Your Help Desk
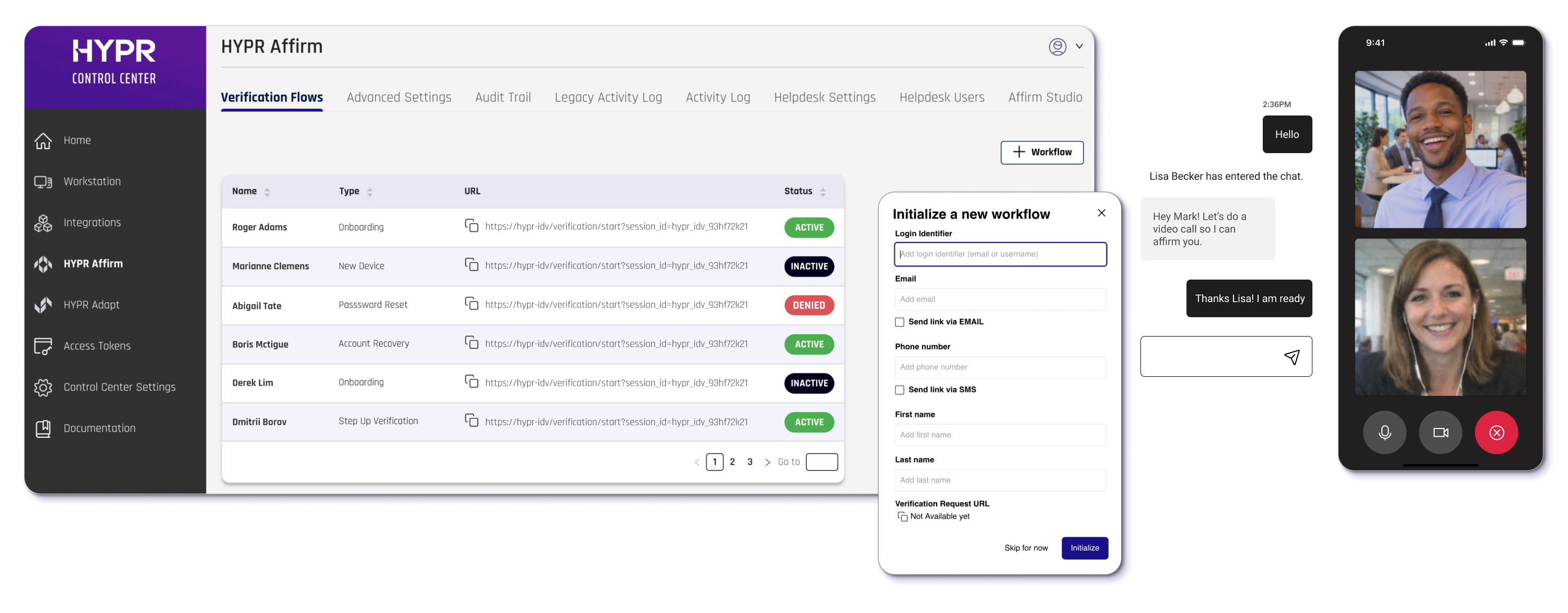
Empower your IT and call center teams with no‑code identity workflows for triaging helpdesk tickets.
Modernize Your Operations Practices
IT operations teams sit at the center of identity, balancing system uptime with a constant stream of resets, access requests, and MFA issues.
What should be routine quickly becomes operational drag. Reset volumes stay high, manual approvals interrupt deeper work, and inconsistent workflows create friction across systems. When something breaks—MFA failures or account recovery—it introduces urgency, risk, and distraction.
At the same time, attackers are increasingly targeting help desks and identity infrastructure, exploiting these moments of friction through social engineering and weak recovery processes.
Learn how leading IT teams eliminate help desk risk and reduce reset-driven attacks without slowing down operations.
→ Download the Help Desk Security Brief
- Granular Access Controls: Ensure agents have exactly the permissions they need—and nothing more—for tighter operational security.
- Improved Session Handling: Clear messaging and smarter behavior when sessions expire, reducing agent frustration and "re-work."
- Custom Messaging Channels: Configure how your team communicates with employees across different channels for a consistent support experience.
- Agent Workflow Enhancements: General usability improvements to streamline agent workflows during identity verification processes.
Up to 98.4%
Reduction in
Account-Takeover Fraud
0
Password Reset Calls
324%
ROI Verified by Forrester®
Inside the Mind of Gen Z Hackers: The Scattered Spider Case
Explore how "Scattered Spider," a group of Gen Z cybercriminals, is reshaping the cybersecurity landscape with bold social engineering tactics. This HYPR blog breaks down who they are, how they operate, and what their rise means for IT and identity security professionals.
What makes this especially relevant for IT and ops teams: Scattered Spider specifically targeted help desks, manipulating support staff through impersonation and social engineering to bypass authentication controls — turning your own workflows against you.
-

HYPR has made the login experience seamless for my team. It was quick and easy to set up for our Okta users, and I appreciate that we can configure it to allow users to log in once at the workstation level, then seamlessly access our SSO without needing additional authentication.
IT User -
HYPR is easy to manage. My end users love using HYPR to login to their computers.
Shane C.Cybersecurity Administrator -
The multifactor solution for iPhone and Android is bar none for corporate environments. Users have one app for all their MFA. Integrates with all of our tools using SAML.
Manufacturing User -
The team at HYPR goes above and beyond to make sure our deployment is successful. The focus on end user experience is key.
Financial Services User -
I like how HYPR works across multiple platforms seamlessly. I use it on a daily basis with my iPhone and work computer.
Automotive User

Request a Demo
Experience passwordless MFA that secures and empowers your business. See what identity verification built for the workforce looks like. Learn how comprehensive Identity Assurance protects the entire identity lifecycle.
Fill out the form to get a demo from an identity security expert, customized around your organization’s environment and needs.






.jpg)

